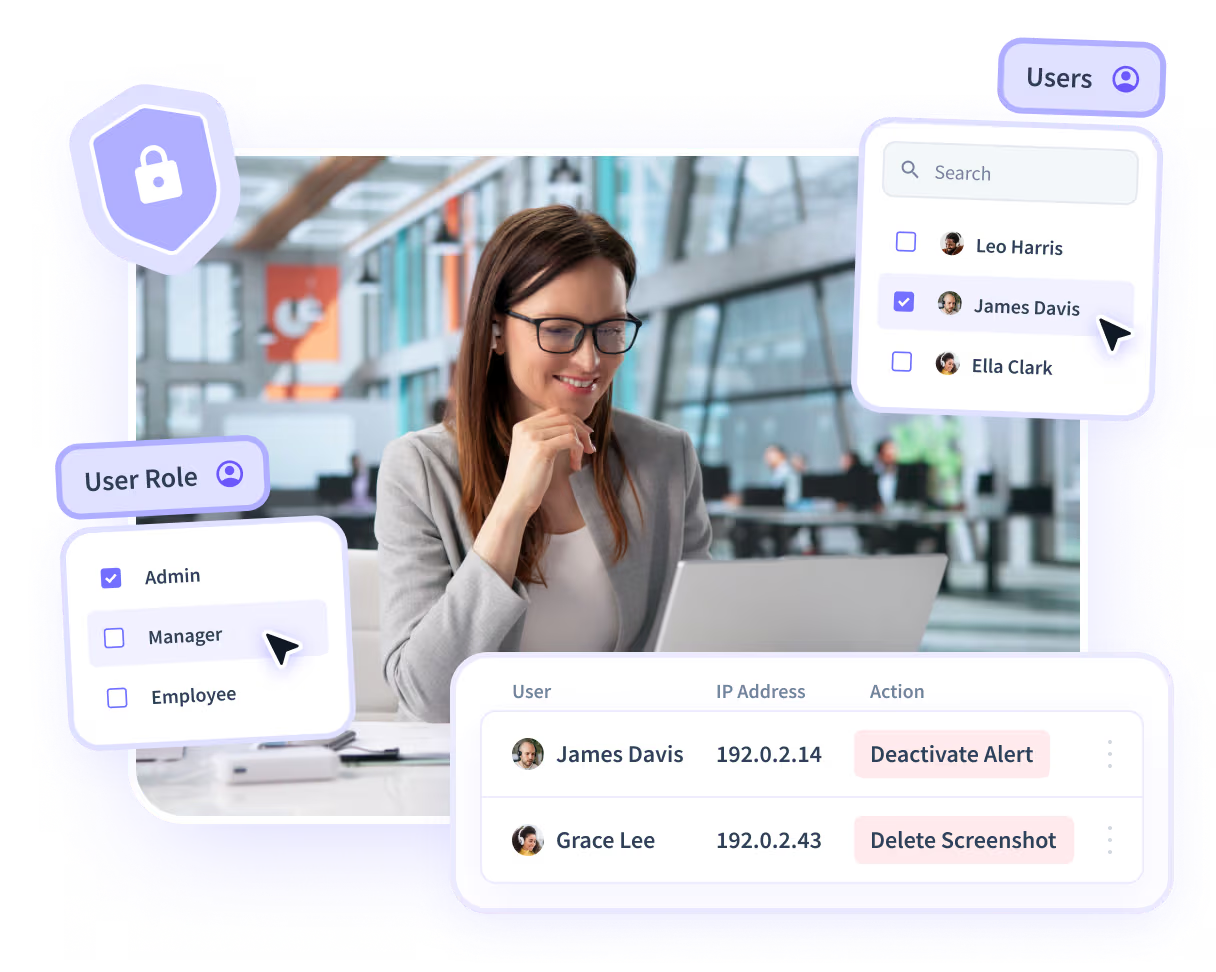
Registros de auditoría: prepárese cuando se cuestione la actividad
Cuando se cuestiona el acceso o los cambios en el sistema, la extracción de registros de varias herramientas ralentiza todo. Los registros de auditoría centralizan la actividad entre sistemas y la vinculan con el trabajo real. Confirme lo que ocurrió sin buscar pruebas.
Cuando surgen preguntas, los registros se dispersan
Los registros de acceso y los cambios en el sistema se encuentran en varias herramientas. Cuando alguien pregunta qué pasó, los equipos se apresuran a recopilar los registros manualmente. Esa demora aumenta el riesgo de cumplimiento y ralentiza el tiempo de respuesta.
Mantenga los registros en un solo lugar y listo
Los registros de auditoría conectan los registros de acceso, los cambios del sistema y la actividad de las aplicaciones en una vista multisistema vinculada al trabajo real. Revise rápidamente las acciones documentadas sin unir los registros.

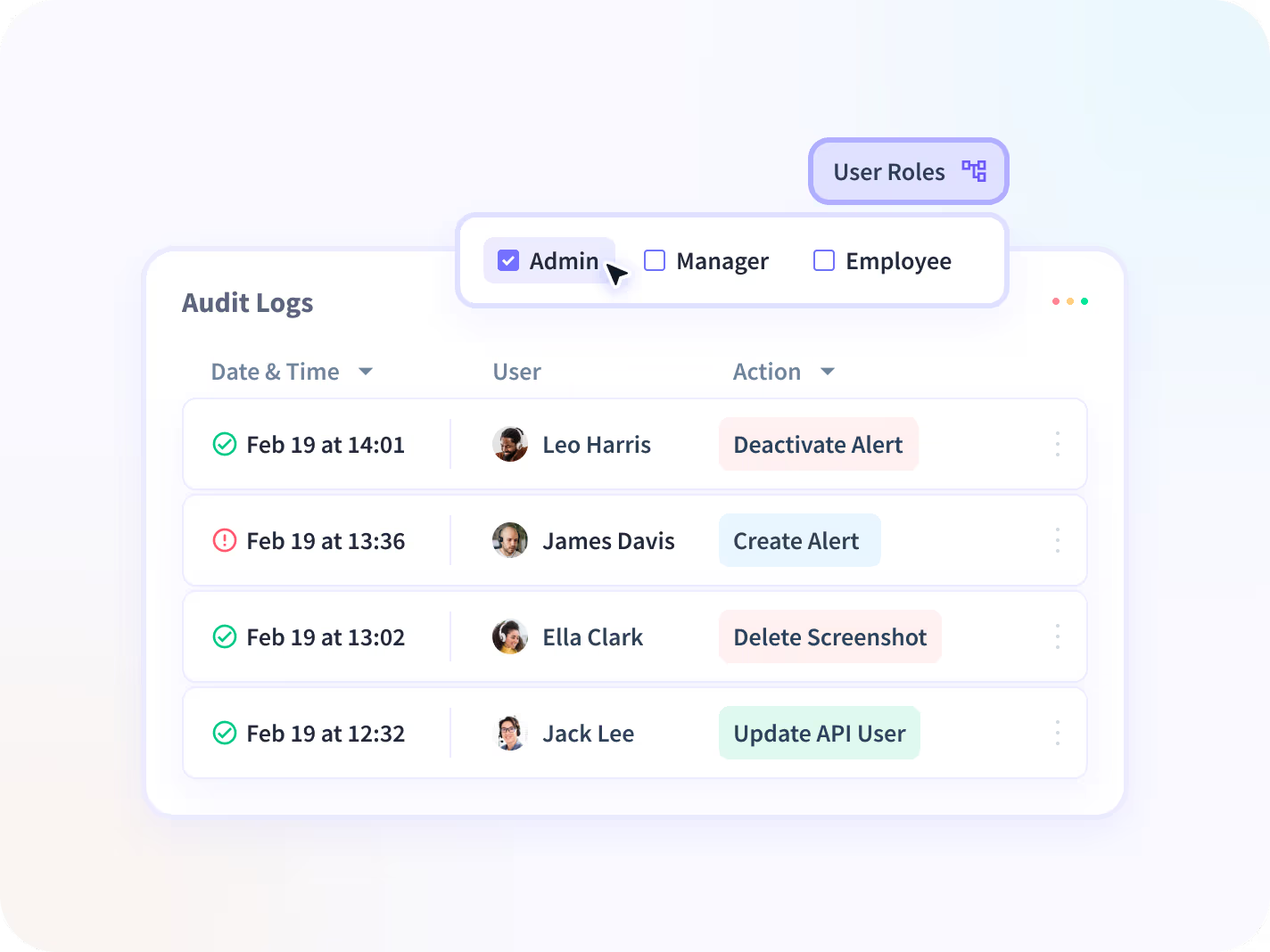
Registros de actividad completos
Acceda al historial y cámbielo en contexto.
Acceso centralizado a los registros
Actividad entre sistemas en un registro.
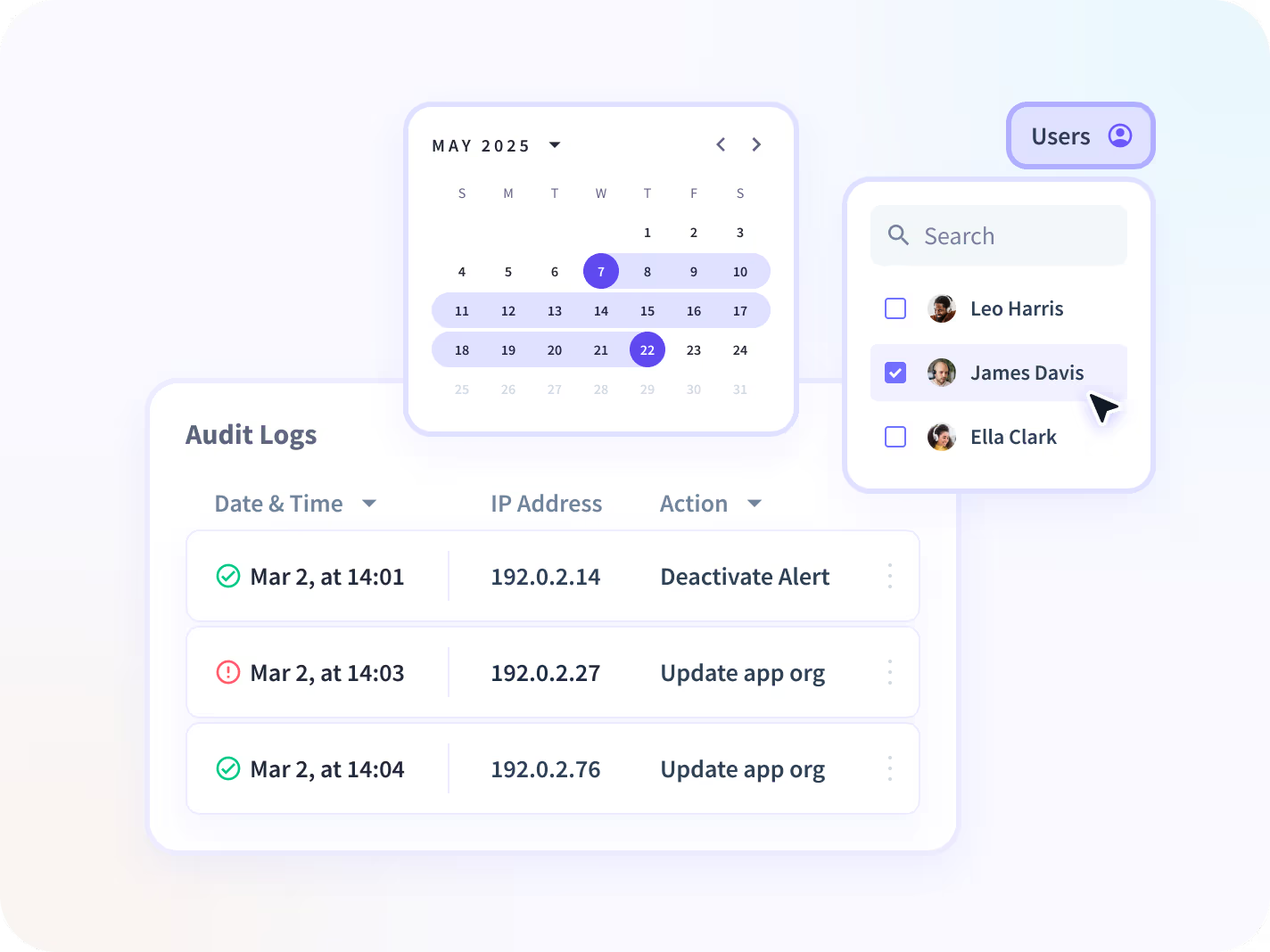
Búsqueda y
Filtrado
Busca acciones por hora, usuario o evento.
Retención e historial
Conserve los registros para auditorías y revisiones.
Exportación e informes
Genere documentación lista para la auditoría.
Casos de uso
Insightful se integra a la perfección con su ecosistema tecnológico
Con más de 50 integraciones disponibles en la plataforma Insightful, conectarse con las principales herramientas de su equipo está a solo un clic de distancia.
Construya un registro defendible
Preguntas frecuentes
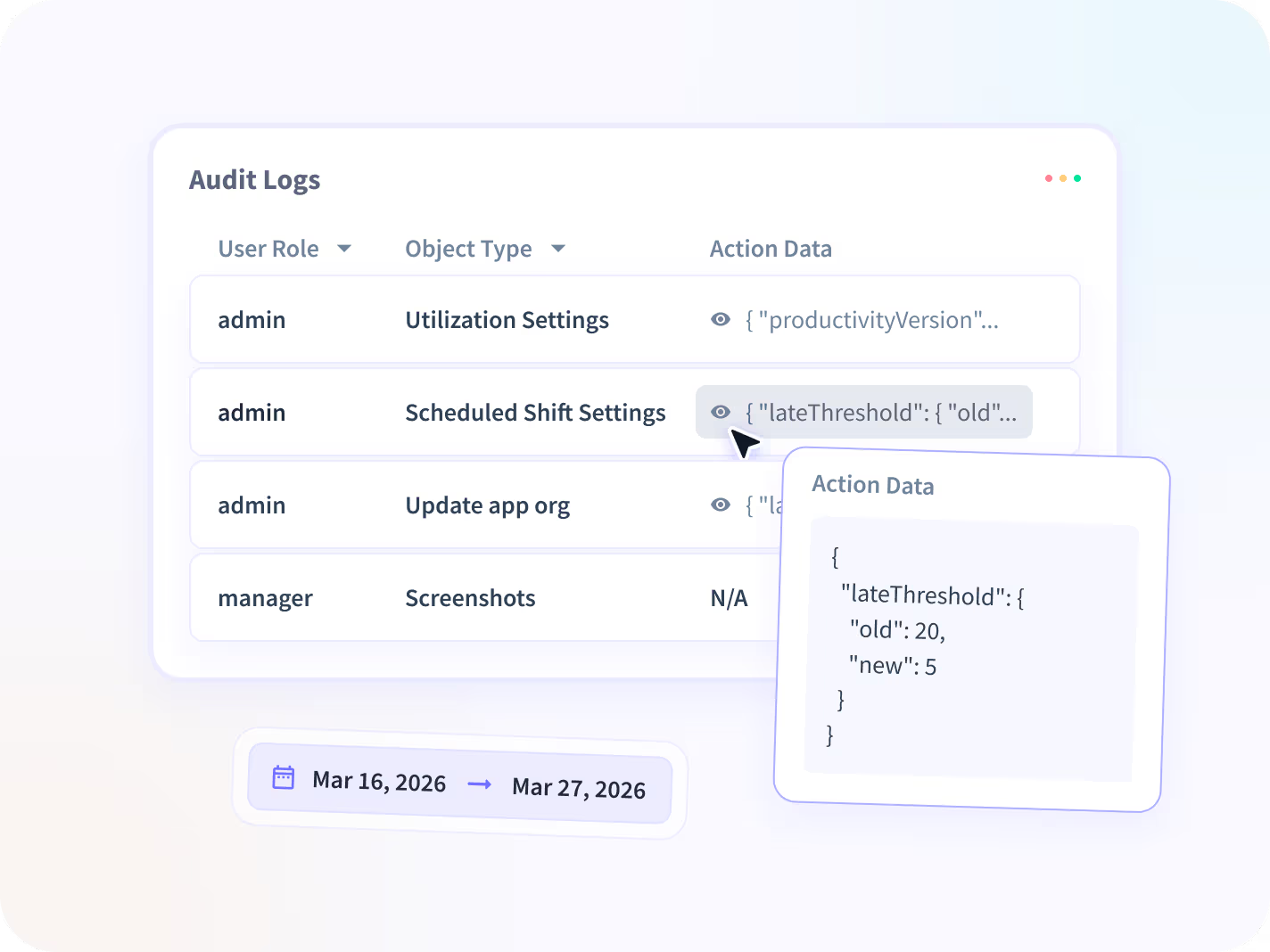
La mayoría de los sistemas generan sus propios registros, pero permanecen aislados dentro de cada herramienta. Los registros de auditoría conectan la actividad entre sistemas vinculada al trabajo real en un registro documentado.
En lugar de cambiar de plataforma, los equipos pueden revisar las acciones en secuencia y responder a las solicitudes de cumplimiento o revisión sin unir las pruebas manualmente.
No. La supervisión tradicional de los registros de auditoría se centra en almacenar o revisar los eventos a nivel del sistema en plataformas individuales.
Los registros de auditoría consolidan los registros de acceso, los cambios del sistema y la actividad de las aplicaciones en todas las herramientas en un registro unificado y defendible. El objetivo no es monitorear por sí solo, sino hacer posible confirmar lo que ocurrió cuando se cuestiona la actividad.
Los registros de auditoría se utilizan cuando los líderes necesitan documentación verificada de la actividad en todos los sistemas. Los factores desencadenantes más comunes incluyen las revisiones de cumplimiento, las auditorías internas, las preguntas de los ejecutivos sobre el acceso o los cambios y las investigaciones de seguridad en fase inicial.
Garantizan que los equipos estén preparados antes de que los problemas se agraven.
Los registros de auditoría proporcionan un historial documentado del acceso y los cambios del sistema en todas las herramientas. Cuando los auditores solicitan pruebas, los equipos pueden generar un registro claro de quién hizo qué y cuándo, sin tener que extraer registros de varios sistemas.
Esto reduce el tiempo de respuesta y reduce la exposición al cumplimiento.
Los registros de auditoría proporcionan una capa de documentación entre sistemas que mantiene la actividad organizada y lista para su revisión.
La ciencia forense se utiliza después de un incidente definido para reconstruir un cronograma de investigación detallado y alineado con el tiempo. Los registros de auditoría garantizan que los registros existan y sean accesibles; la ciencia forense permite un análisis más profundo de los incidentes cuando es necesario.






